Photography Certificate Of Authenticity Template. Edge TPU ASIC designed to run ML inference and AI at the edge. Apigee Healthcare APIx FHIR API-based digital service manufacturing. Cloud Code IDE assist to write, run, and debug Kubernetes purposes.
Open Source Databases Fully managed open source databases with enterprise-grade assist. Mainframe Modernization Automated instruments and prescriptive steerage for shifting to the cloud. Telecommunications Hybrid and multi-cloud companies to deploy and monetize 5G. And later within the AuthZ policy you’ll have to create an internet authentication rule that references an MDM portal. Disadvantages to this deployment are that at the time of this writing EAP-Chaining is a Cisco proprietary methodology that requires the AnyConnect NAM and is as such a Windows-only feature. If other platforms are required, OSX or any other mobile OS, one other methodology must be used.
Please observe that the choice to accept particular credit recommendations is as much as each establishment and isn’t assured. In addition to expert-led training and hands-on tasks designed to prepare you for a job, you will get entry to interview suggestions, mock interviews and resume constructing workshops, profession teaching sessions and extra. You’ll additionally be in a position to connect with over one hundred thirty U.S. employers who’re looking for candidates who’ve completed a Google Career Certificate. One of the most thrilling parts of being a data analyst is the number of opportunities out there.
For extra information about utilizing CEL, see Using CEL. Secret Manager Store API keys, passwords, certificates, and different sensitive data. Databases Migrate and handle enterprise information with safety, reliability, high availability, and fully managed knowledge services.
These particular authentications happen independently and, the place possible, we advocate you perform each. Advantages in deployment of this system are numerous. X509-type authentication is taken into account the gold commonplace for community authentication. The disadvantages of this methodology are merely that the organization selecting to deploy this must preserve an inner PKI that permits for certificate distribution to client machines for authentication. If a PKI doesn’t exist, one have to be designed, and deployed previous to this architecture being chosen. •Computer-only authentication permits for access solely to WSUS, AV servers, and domain controller companies.
Don’t fear when you change your thoughts or you’re not pleased with the results. Unlimited Downloads From $16.50/month Get access to over a million creative belongings on Envato Elements. Brenda Barron is an teacher for Tuts+ specializing in enterprise and web design matters.
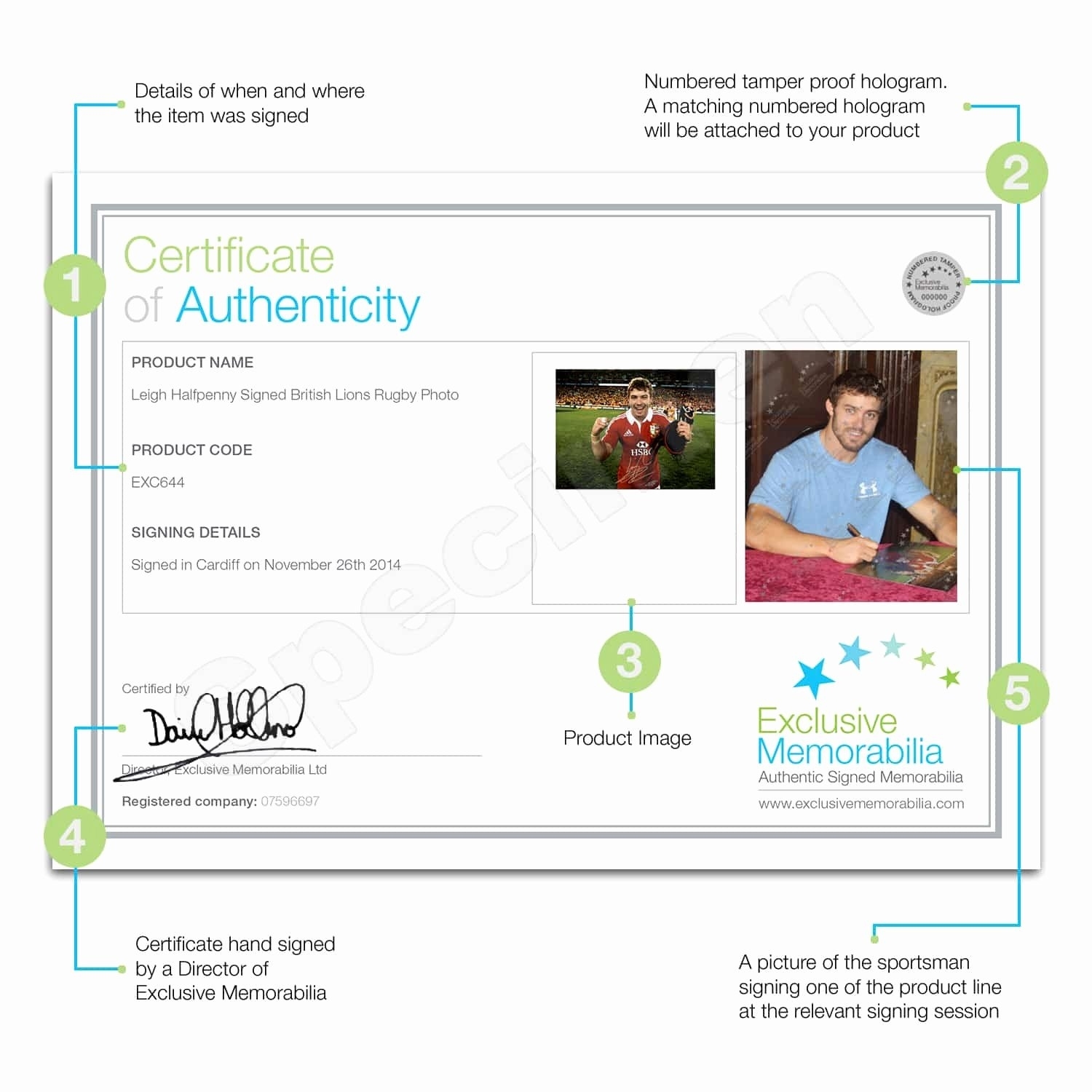
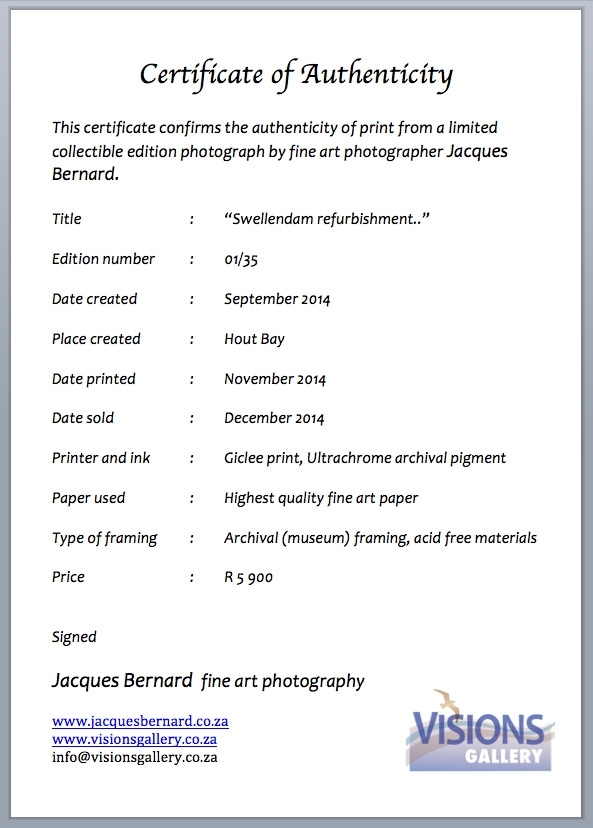
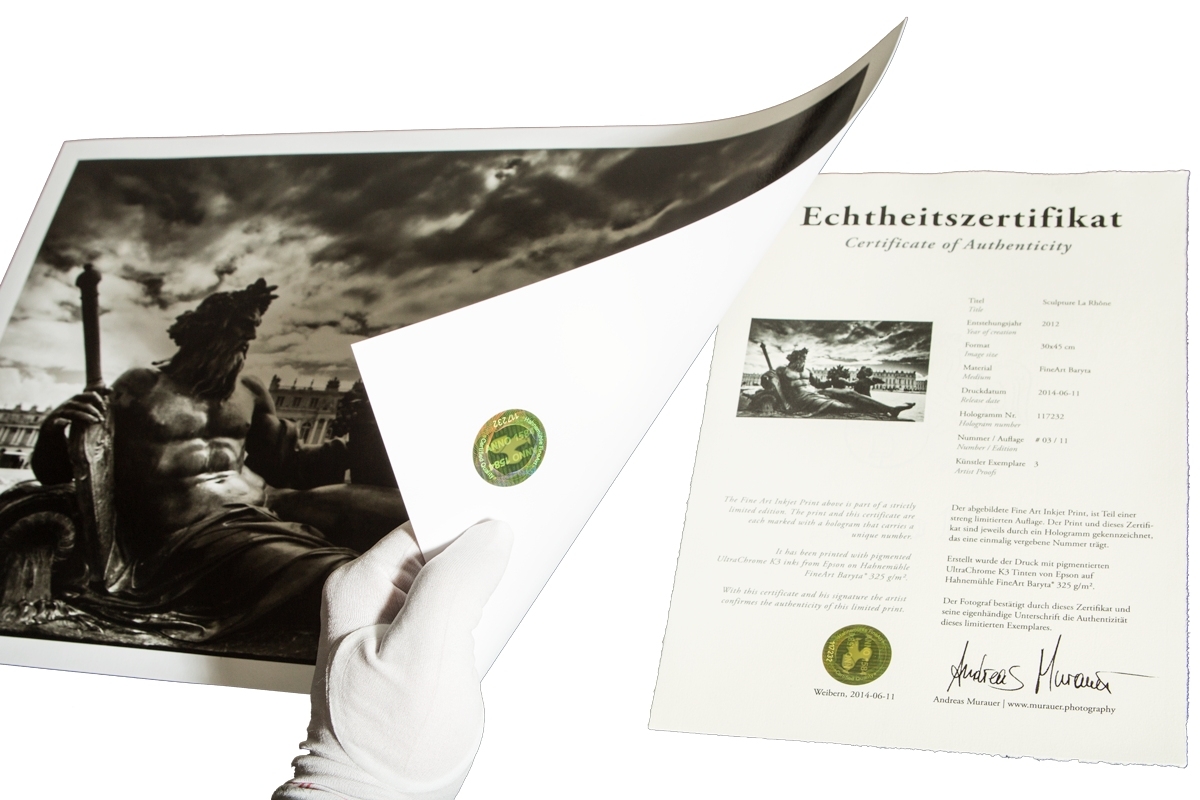
Welcome to Printed Corporate, the place a devoted group awaits to assist you and your small business. Fields might differ depending on the type of certificate for which you’re creating a Photography Certificate Of Authenticity Template. Perform the next steps to request a certificate for the NPS server. Placing NPS servers behind a devoted network load balancing equipment isn’t typically required. However, there are some deployment scenarios where doing so can present necessary advantages. Create better projects quicker with limitless downloads of fonts, mockups, shows and extra.
Create Sample Photography Certificate Of Authenticity Template
She additionally writes and edits for quite a lot of different companies throughout many topics including small enterprise, WordPress, and marketing. She holds a BA in English and has over a decade of expertise crafting blog posts, articles, white papers, and extra for clients throughout many industries. When not writing, yow will discover her spending time her with household, singing, taking half in piano, and portray.
They can end up being a valuable a part of your skilled toolkit. Traditionally certificates are horizontal, but that’s changing. Now people use vertical certificates simply as a lot as they use horizontal certificates templates. Vertical certificates templates stand out among the many conventional horizontal certificate templates as being unique. Here’s the Photography Certificate Of Authenticity Template download we’ll use in this walkthrough. Customize the editable certificate template in Microsoft Word, Adobe Photoshop, or Adobe Illustrator.
Let’s take a second to talk about why doing machine authentication along with person authentication is essential for a good user experience . •The SAN of an ISE-issued certificates have the MAC tackle of the device the certificate was issued to. •MDM- or ISE-issued certificates usually have the username merely as the widespread name of the certificate. •AD-issued certificates usually have the username/hostname of the certificate in the SAN field as the UPN or DNS name of the PC. •Disable detachable media access to make removing of key info directly from a system tougher.
Image of Awesome Photography Certificate Of Authenticity Template
√ 20 Certificate Of Authenticity Photography ™ | Dannybarrantes Template regarding Photography Certificate Of Authenticity Template.
Certificate Of Authenticity Photography – Planner Template Free throughout Photography Certificate Of Authenticity Template.
5 Template Certificate Of Authenticity For Art 69837 | Fabtemplatez pertaining to Photography Certificate Of Authenticity Template.
Certificate Of Authenticity Photography – Planner Template Free with regard to Photography Certificate Of Authenticity Template.